The PCI Software Security Framework was introduced by the PCI SSC last year to improve the security of card payment software. Under this framework there are two separate standards:
- Secure Software Lifecycle Standard – companies operating a secure SDLC validated against the standard
- Secure Software Standard – software validated against the standard
The first assessment under this framework was announced with great fanfare on August 12th, 2020. We’re now 8 months out from that date, so it seems a good time to take a look at the current rates of adoption for the standards under the new framework.
Contents
Why should people use these standards?
Software security has always been a key concern in the secure payments space. Many years ago, the PCI SSC released a software security standard called the Payment Application (PA) DSS. The intention was that companies using PA DSS-validated software could streamline their PCI DSS compliance. For all software covered by the PA DSS, all a QSA would need to do is review the software listing, ensure the version matched, and consider that aspect of the business compliant.
Over time issues were found with the old standard, and it was decided to create a new software security framework rather than trying to adapt the PA DSS itself. As a result, the PA DSS is currently being wound down, with no new submissions permitted and final program shutdown in 2022. The replacement framework is the Software Security Framework, and the standards against which companies are assessed are the two listed above.
Industry Adoption
It has been suggested that one of the perceived issues with the PA DSS was low levels of adoption in the industry. Because the PA DSS itself is intended for a very limited payment application, it was not really applicable for bigger software suites like issuing platforms or payment switches. There was no incentive for these vendors to go through PA DSS, but with low adoption and interest it was hard to refine the standard to make it more encompassing.
That’s the position from which the Software Security Framework starts. A good measure, if not the key measure, of the success of the new framework is rate of adoption in the industry. It’s still early days, but the new standards have been around for over half a year. For all that time, there has been at least one QSAC (Coalfire) able to conduct assessments.
I have no visibility into Coalfire’s business, nor any other QSAC for that matter. It may be that there are hundreds of these assessments being done right now, preparing for a great “Cambrian explosion” of validated payment software and companies. As of right now, the only visibility we have into the success of this framework program is through looking at validated solutions.
Validated Solutions
Fortunately, the PCI SSC publishes lists of validated payment software and software vendors on their web site. To get visibility into the current performance of the Software Security Framework in the market, we can look to the set of validated solutions available.
Unfortunately for the PCI SSC, the number of validated software solutions and software vendors is still very small. These assessments will all take time to conduct, and are complicated by being the first assessments conducted by each QSAC under the new framework. Because of this it’s still far too early to gauge the likely success of the new Software Security Framework in the market.
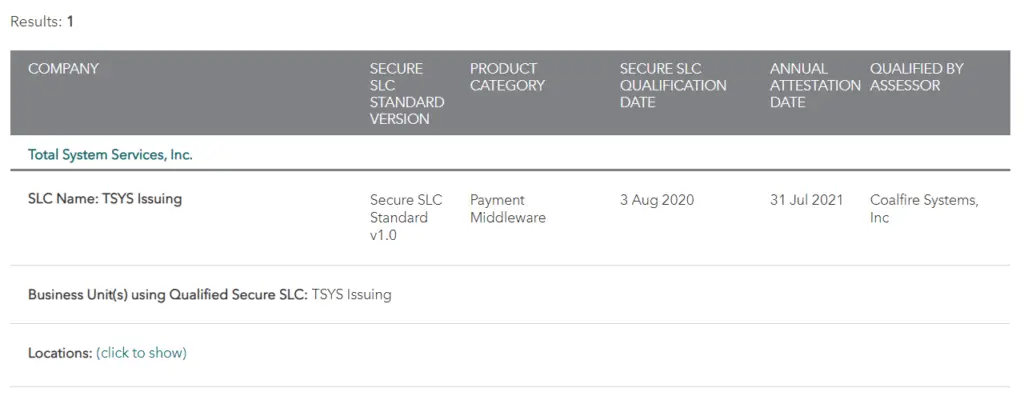
As noted previously, Coalfire completed the first SSF assessment of a software vendor in August 2020. As of writing in April 2021, that company (TSYS) is still the only company listed as validated on the PCI SSC website:
The situation is similar for software validated under the SSF, with just two listings showing as of writing.
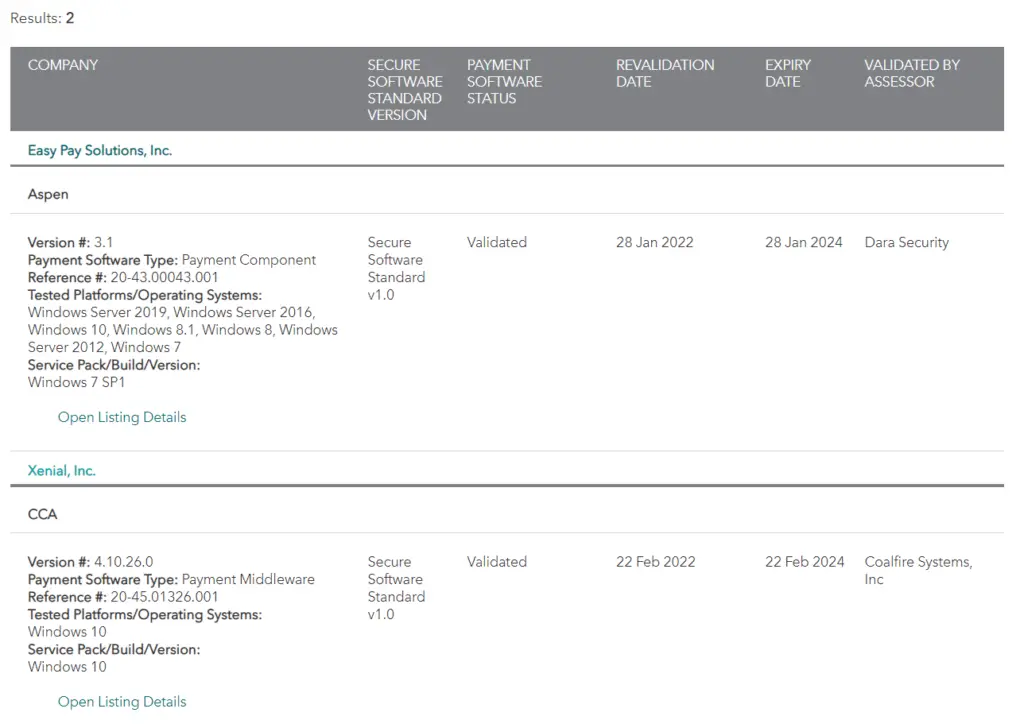
Note that both of these are validated to run on Windows 10. Not to disparage Windows 10, but it’s not a server OS. No software has yet been validated which is intended to run as a core processing or switching component in the payment network. This may be partly due to the sheer scale of these systems vs. desktop components, and so requiring a longer time to actually validate. But it is of interest that the initial software to be validated typically had a more restricted set of requirements than much of the payments ecosystem.
SSF Assessors
We can also gauge market interest differently by looking at the number of Software Security Framework Assessors available. That is, the number of QSACs who have paid to undergo the training and to register as assessors under the Secure Software Framework.
As of writing, only two assessors, Coalfire and Dara Security, have successfully completed assessments under this new framework. However, if we look at registered assessors the picture looks a little more rosy. There are currently 31 separate firms listed as being able to perform SSF assessments. That’s a little under 10% of the total number of PCI DSS QSACs:
If each of these has just a few SSF-related deals in their pipeline, that’s potentially over a hundred validated solutions and providers in the market soon.
Uptake Tracker
The rate of uptake of this standard over time will good feedback on the likely success of the new framework in the market. Because of this I’m publishing a PCI Secure Software Framework Uptake Tracker. This shows month-on-month adoption of validated software and companies.
